FTP stands for File Transfer Protocol, which relies on client/server technology. It is a software application that transfers files between systems. The FTP protocol was developed in the 1970s and is one of the most commonly used protocols to transfer data between computers over the Internet.
However, despite being an old methodology, users still find it to be one of the best and most commonly used protocols, and users enjoy using it for uploading and downloading files in their day-to-day work. Setting up an FTP server on Linux is generally quite simple.
Essentially, this FTP software package performs two (2) basic tasks: 'Put' and 'Get. When "Put" is used, files will be copied from a local computer to a remote computer, while "Get" handles the opposite. FTP daemon 'vsftpd' is a server component that constantly listens for FTP requests from remote clients. It manages the log-in process and establishes the connection when a request is received. By default, it works with port 21 and executes any commands sent by the FTP client during the session.
This step-by-step guide will teach you how to install and configure FTP servers (vsftpd) for users with local accounts to upload/download files in Rocky Linux 8.4. Similarly, this guide can be used with RHEL, CentOS, Fedora, Ubuntu, Debian, and Ubuntu with a few minor modifications.
FTP Access methods:
Generally, two methods are used to access FTP servers:
1. Anonymous = A remote client can access the FTP server by using the default user name "ftp" or "anonymous" as a user name and sending an email address as a password.
2. Authenticated = Users need to have accounts and passwords. Based on the permissions granted, they can access files and directories.
Prerequisites :
Operating System : Rocky Linux / RHEL /CentOS /Fedora package : vsftpd.x86_64 User account : root user or user account with sudo privileges Recommended to run all the administrative commands as with sudo privilege instead of root.
Difficulties in setting up sudo users? Click here to find the steps.
My Lab Setup :
My lab setup consists of two machines. The server runs on Rocky Linux 8.4, while the client runs on Ubuntu 18.04 LTS.
FTP Server: Operating System : Rocky Linux release 8.4 (Green Obsidian) Hostname : ftp01.linuxteck IP Address : 192.168.1.100
FTP Client: Operating System : Ubuntu 18.04.5 LTS Hostname : john-H81M-WW IP Address : 192.168.1.200 SSH client : An active ftp client like " Terminal for Linux/Mac and Filezilla for Gui"
To set up an FTP server, you need a command-line/Terminal console. This tutorial assumes you have SSH access to the remote server where the FTP server will be installed. If you're having trouble connecting to a remote server through SSH, here's a guide to connecting to a remote server "10 basic and useful ssh client commands in Linux."
Note:
In this lab exercise, you will learn how to set permissions for local users to access their alternative home directories, as well as how to set the permissions to the specific directories via chroot to transfer files between computers. In case you need to set up an anonymous FTP server for downloading. This link will walk you through the step-by-step process on how to set up Anonymous FTP in Rocky Linux 8.4.
Step1: Install FTP (vsftpd) package
Note:
The installation command might differ based on the Linux distribution you choose. If you are running Rocky Linux, RHEL, CentOS, or Fedora, then run the following command to install VSFTPD:
To manage software packages on RedHat-based Linux systems, you can use YUM, DNF, and RPM. I will go with DNF. In case you encounter any trouble using YUM or DNF, refer to the links below for help.
For Yum - YUM Guide for Beginners with 15 Examples
For DNF - DNF Guide for Beginners with 20 Examples
Note:
You should first update the OS to the latest version, then install the FTP server. The following commands can be used to install the vsftpd package:
$ sudo dnf update
Note:
As soon as the installation command is executed, you will be asked to confirm the installation by choosing "y" or "n.". Just press 'y' to continue. It is even possible to install the packages without having a confirmation prompt by adding '-y' to the end of the above command. There are 192 packages in our system that need to be updated. I've copied only a few lines below in the screenshot for your understanding. Upon completion of this OS update, you can install the vsftpd package for our FTP server using the following command:
$ sudo dnf install vsftpd
Note:
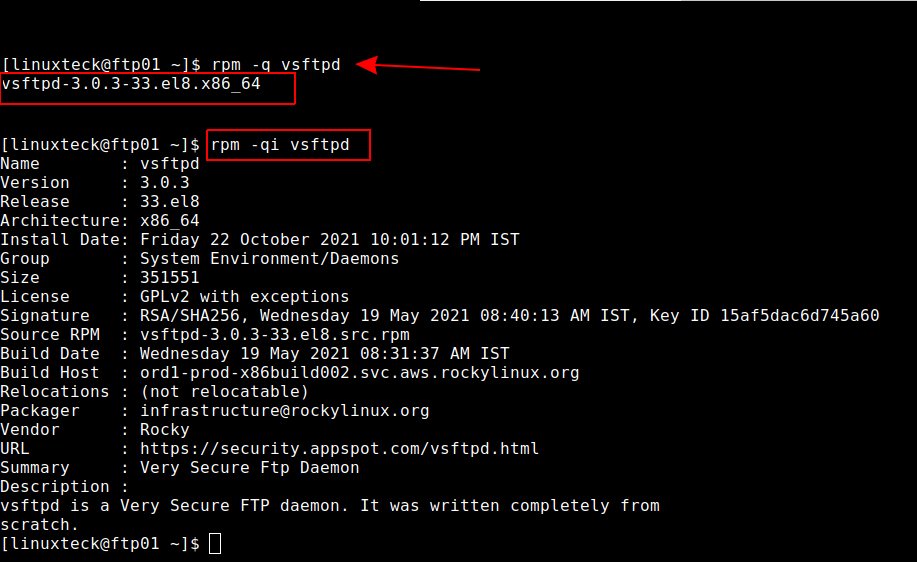
To continue, press 'y'. After completing the installation, you can verify the installation by running the RedHat command "rpm -q ". It will inform you whether the package was successfully installed or not. The '-i' flag, can also be used to get more information from the package.
Tip:
For Ubuntu/Debian, you need to run the following command:
$ sudo apt-get install vsftpd -y.
Note:
As the name suggests, VSFTPD stands for "Very Secure FTP Daemon". It is a universal FTP daemon developed under a GPL license for many Unix-based systems. Even though it is small in size, this FTP package contains an impressive amount of features compared to other FTP servers. Check them out below.
- Virtual IP configurations
- Virtual users
- Standalone or inetd operation
- Powerful per-user configurability
- Bandwidth throttling
- Per-source-IP configurability
- Per-source-IP limits
- IPv6
- Encryption support through SSL integration
Note:
Use the following command to 'start' the FTP daemon and 'enable' it to start the service automatically after every reboot of the server and finally check the 'status of the services.
$ sudo systemctl start vsftpd
$ sudo systemctl enable vsftpd
$ sudo systemctl status vsftpd
Note:
As a result, the FTP service started properly if the status showed "active" (running). You can check the port number using the 'netstat' command. It only listens on port 21. Below is the output.
$ sudo netstat -tulnp | grep vsftpd
Output: tcp6 0 0 :::21 :::* LISTEN 1303/vsftpd
Step 2: Configuring VSFTPD
Note:
The next step will be to configure the FTP server for local users and set up authentication and permissions based on the access. The main configuration file for the FTP service can be located at "/etc/vsftpd/vsftpd.conf". This file can be customized by editing it correctly. Keeping a copy of your original (default) configuration is always a good idea. If the new configuration does not work, it is easy to turn it back to the default configuration.
You can copy the default configuration file with the "cp" command.
$ sudo cp /etc/vsftpd/vsftpd.conf /etc/vsftpd/vsftpd.conf.bak
Note:
The configuration file can be edited in a text editor. I use the "vi" text editor. This file contains instructions. Some of them are commented on, but others aren't. Each line contains a hash (#) that identifies it as a comment. By default, the demon ignores those lines (instructions). To enable those instructions in the config file, you need to remove the hash (#) sign.
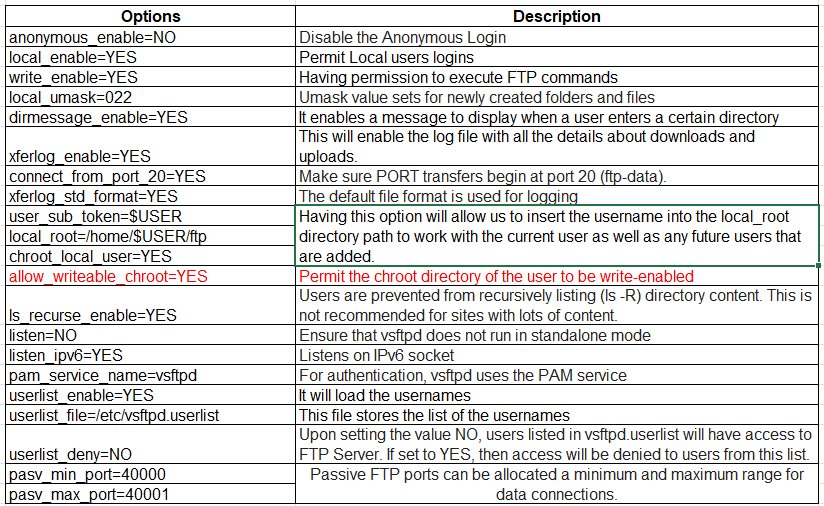
To configure a local authenticated FTP server (vsftpd), we need to modify and add the following lines to the vsftpd configuration file.
Note:
The configuration file has several instructions/parameters. As a first step, we will only make the changes mentioned in the screenshot above to create a local authenticated FTP server. Once, you have made the changes to vsftpd.conf, you can save the file. To comply with your requirements, you can include additional instructions in the file.
$ sudo vi /etc/vsftpd/vsftpd.conf
# Allow anonymous FTP? (Beware - allowed by default if you comment this out). anonymous_enable=NO # Uncomment this to allow local users to log in. local_enable=YES # Uncomment this to enable any form of FTP write command. write_enable=YES # It enables a message to display when a user enters a certain directory dirmessage_enable=YES # Activate logging of uploads/downloads. xferlog_enable=YES #Make sure PORT transfers begin at port 20 (ftp-data). connect_from_port_20=YES #The default file format is used for logging xferlog_std_format=YES #Having this option will allow us to insert the username into the local_root directory path to work with the current user as well as any future users that are added. user_sub_token=$USER local_root=/home/$USER/ftp chroot_local_user=YES #Permit the chroot directory of the user to be write-enabled allow_writeable_chroot=YES #It will load the usernames userlist_enable=YES #This file stores the list of the usernames userlist_file=/etc/vsftpd.userlist #Upon setting the value NO, users listed in vsftpd.userlist will have access to FTP Server. If set to YES, then access will be denied to users from this list. userlist_deny=NO #Users are prevented from recursively listing (ls -R) directory content. This is not recommended for sites with lots of content. ls_recurse_enable=YES #Passive FTP ports can be allocated a minimum and maximum range for data connections. pasv_min_port=40000 pasv_max_port=40001
Save and restart the vsftpd service.
$ sudo systemctl restart vsftpd
Warning:
If we enable chroot for local users "chroot_local_user=YES", their home directories will be placed in a chroot jail after login, which means the VSFTPD demon will block writing permission to the user's home directory for security reasons. To disable this option, we can include the parameter "allow_writeable_chroot=YES" in the vsftpd.conf file. However, we do not recommend disabling writeable permissions since it could lead to a security breach. Depending on your needs, you can either enable it or disable it.
In the following guide, we will show you how to create a local directory (FTP) that a local user can access safely without removing their existing privileges (writable) from their home directories.
Step 3: Set up FTP User's and their Local (Home) Directories
Note:
Using the following useradd command, we can create a new FTP user to test the FTP server.
$ sudo useradd linuxteck
$ sudo passwd linuxteck
Note:
You must add the newly created user to /etc/vsftpd.user to gain access to the FTP server. You can accomplish this by running the echo command. By specifying the '-a' flag, you can append a file.
$ echo "linuxteck" | sudo tee -a /etc/vsftpd.userlist
Note:
The next step is to create two directories and set their permissions. This primary directory stores a user's files; others do not have writeable permissions for it. A sub-directory, which will be created under the parent directory, can be used to upload/download files.
$ sudo mkdir -p /home/linuxteck/ftp/files
Note:
With the '-p' flag, we can create subdirectories within the parent directory. By default, the '-p' flag creates a parent directory if it does not already exist, and then it creates all the sub-directories in a specified directory structure. Also, make sure the permissions are set correctly. Due to security concerns, we will change the ownership of the FTP directory to "nobody" and remove the write permissions.
$ sudo chown nobody: /home/linuxteck/ftp
$ sudo chmod a-w /home/linuxteck/ftp
Note:
Similarly, we must set the appropriate permissions to the second directory.
$ sudo chown -R linuxteck: /home/linuxteck/ftp/files
$ sudo chmod -R 750 /home/linuxteck/ftp/files
Let's verify the permissions:
$ sudo ls -la /home/linuxteck/ftp
Output: dr-xr-xr-x. 3 nobody nobody 19 Nov 21 12:47 . drwx------. 5 linuxteck linuxteck 142 Nov 21 23:42 .. drwxr-x---. 3 linuxteck linuxteck 73 Nov 22 23:26 files
Note:
Next, we can create a dummy file in the directory that the client can use for testing.
$ echo "ftp_test_File" | sudo tee -a /home/linuxteck/ftp/files/ftptest.txt
Step 4: Enable firewall services
Note:
You need to add rules to the firewall to allow ports 20-21 for FTP data and ports 40000-40001 for vsftpd passive communication by using the following firewalld command. If you have difficulties configuring firewalls, click here to learn the steps for how to configure firewall-cmd commands in Linux.
$ sudo firewall-cmd --permanent --add-port=20-21/tcp
$ sudo firewall-cmd --permanent --add-port=40000-40001/tcp
$ sudo firewall-cmd --reload
Note:
Finally, we must restart the vsftpd service and check its status before performing tests.
$ sudo systemctl restart vsftpd
$ sudo systemctl status vsftpd
Step 5: Test FTP Access with FTP client (FileZilla) & Command-Line
Note:
The FTP server has been successfully configured to be accessible only to local users with proper authentication. In our example, only one user has access to the FTP server named "linuxteck". First, we will test by logging in as an anonymous user, followed by another local user, and finally by logging in as the permitted user.
Our testing will consist of two methods: a command-line interface and a third-party FTP tool. Let's start with a command-line interface. Let's connect to our FTP host so we can see the FTP daemon response. Sometimes when you execute the ftp command for the first time, an error may occur like "bash: /usr/bin/ftp: No such file or directory"; This means that the FTP client package is not installed, by default. You can install it easily by using the following command. Depending on the Linux distribution, you may need to modify this command. In our case, we are using Ubuntu 18.4.
$ sudo apt install ftp
Note:
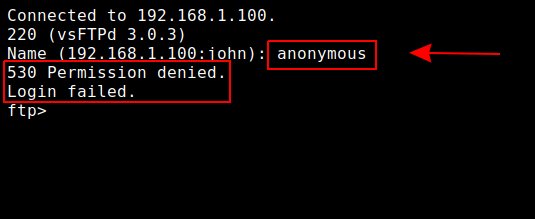
The following command will connect you to the server. If asked for a user name, type "ftp" or "anonymous" and press enter. Once you do, you will see a 530 Permission denied message. It means anonymous users are not allowed.
$ ftp 192.168.1.100
Output:
Note:
In order to exit FTP mode, simply type "bye" or "exit" as shown below. Next, try with another local user named "john".
ftp> bye
$ ftp 192.168.1.100
Output:
Note:
Now, try with an authorized user named "linuxteck".
$ ftp 192.168.1.100
Output:
Note:
To test passive mode, we must be sure that all client commands are being sent to the server correctly, such as "ls" and "get."
ftp> ls
Output:
Note:
We will also try to download the dummy file "ftptest.txt" locally. Start by navigating to the "files" directory with the "cd" command and then use the "get" command to download the file."
ftp> cd files
Output:
250 Directory successfully changed.
ftp> ls
Output: 200 PORT command successful. Consider using PASV. 150 Here comes the directory listing. drwxr-x--- 3 1001 1001 73 Nov 22 17:56 files 226 Directory send OK.
ftp> get ftptest.txt
Output:
local: ftptest.txt remote: ftptest.txt
200 PORT command successful. Consider using PASV.
150 Opening BINARY mode data connection for ftptest.txt (14 bytes).
226 Transfer complete.
14 bytes received in 0.00 secs (30.0481 kB/s)
Note:
As you can see from the output, the download was successful, and the file was downloaded to your computer. Similarly, we will use the "put" command to upload a file from your local system to the FTP server.
Ensure you should only use the "files" directory."
ftp> put kids.karakastechnologies.com
Output:
local: kids.karakastechnologies.com remote: kids.karakastechnologies.com
200 PORT command successful. Consider using PASV.
150 Ok to send data.
226 Transfer complete.
5439840 bytes sent in 0.47 secs (11.1043 MB/s)
ftp> ls
Output:
200 PORT command successful. Consider using PASV.
150 Here comes the directory listing.
-rw-r--r-- 1 0 0 14 Nov 21 14:25 ftptest.txt
-rw-r--r-- 1 1001 1001 5439840 Nov 21 15:29 kids.karakastechnologies.com
226 Directory send OK.
ftp>
Note:
The test results have been excellent. It has been verified that only the permitted user named "linuxteck" can log in successfully and be allowed to download and upload files successfully. Now you can leave FTP mode by typing the "bye" or "exit" command."
ftp> bye
Output:
221 Goodbye.
Note:
We'll now install FileZilla to access the server. Depending on your Linux distribution, you can use the appropriate command to install FileZilla. For our testing environment, I will install FileZilla on Ubuntu with the following command:"
$ sudo apt-get install filezilla
Note:
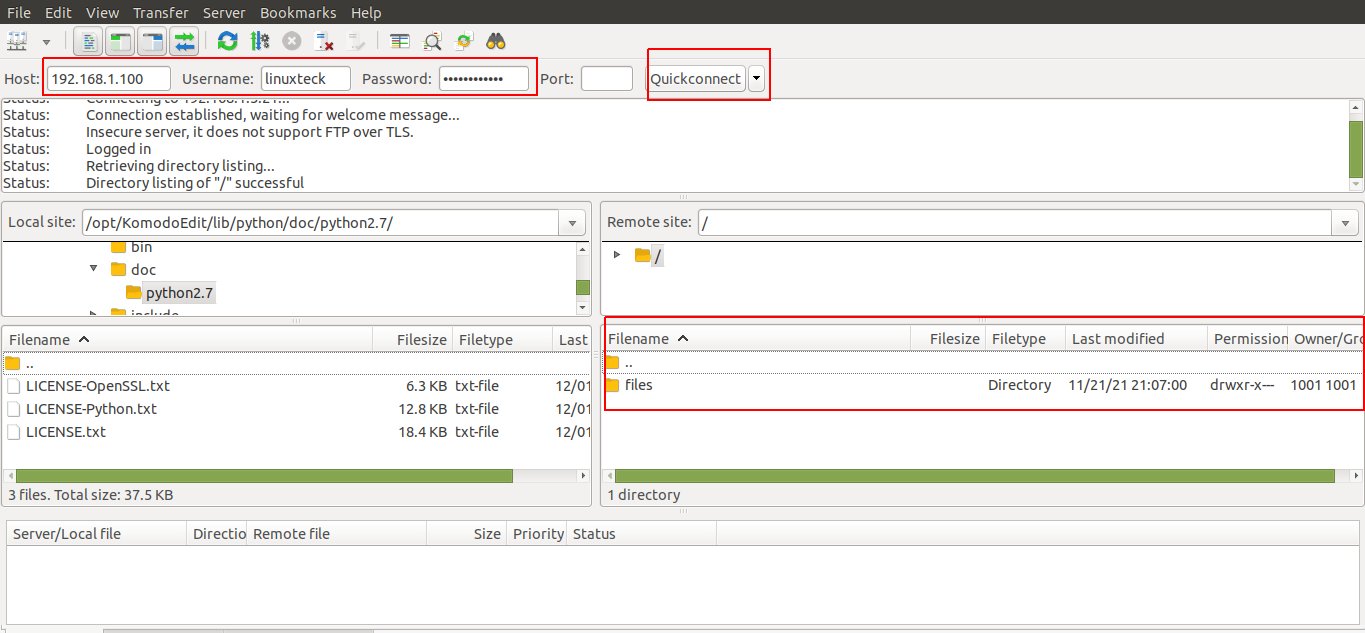
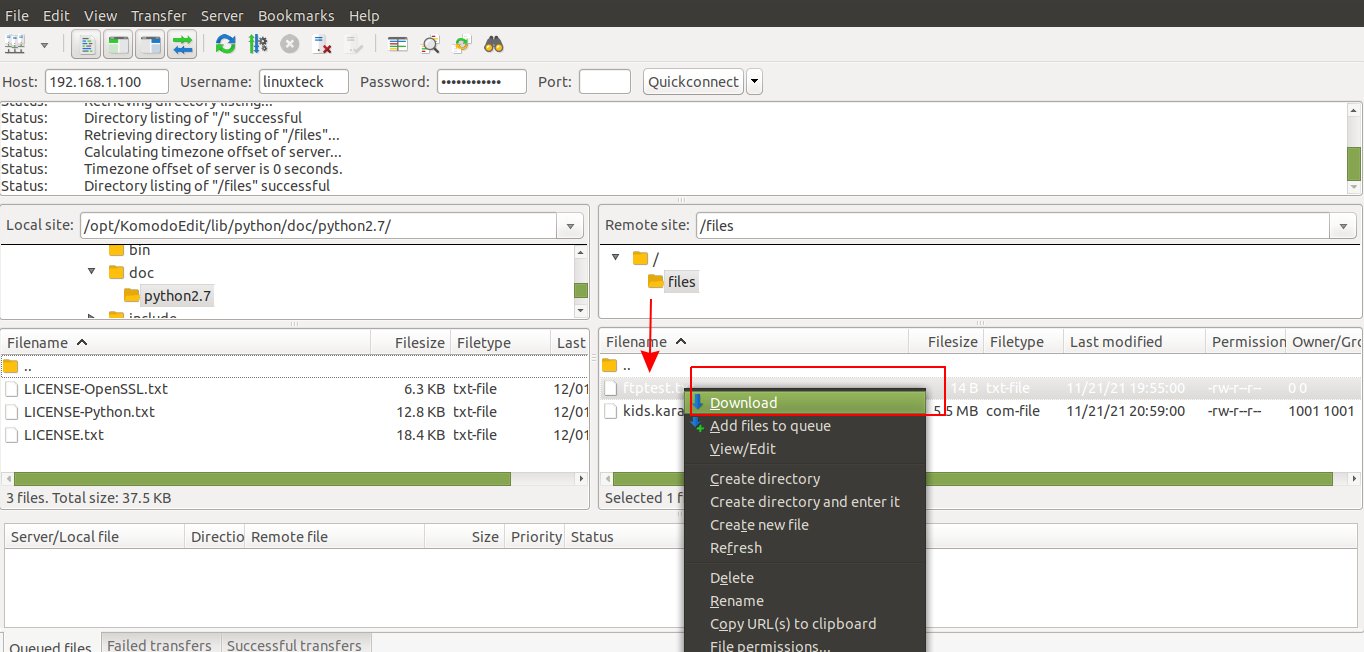
After you have successfully installed FileZilla, you should open it, enter the IP address of the FTP server and type the username as 'linuxteck' and enter the password and then click on quick connect to the FTP server. You can now see the "files" directory on the FTP server, as shown in the following screenshot."
Note:
You can now open the files directory and check out our ftptest.txt file. To download the file, right-click on the file and choose to download it to your local drive."
Note:
That's it! We have completed the installation and configuration of the FTP (vsftpd) Server on Rocky Linux 8.4 to permit or restrict a user's access to their home directory and to restrict downloads and uploads from specific directories via chroot."
Step 6: Disabling shell access to FTP user accounts
Note:
Every user account on Linux is automatically set up to allow SSH access, which is one of the biggest security vulnerabilities. FTP users do not often require shell access. Hence, you can disable it. It is purely optional. Depending on your needs, you can enable or disable shell access. In our exercise, I am going to disable shell access for the user named "linuxteck".
For a better understanding, let's first log in with the user "linuxteck" via ssh, then we will disable it."
$ ssh linuxteck@192.168.1.100
linuxteck@192.168.1.100's password:
Output:
Activate the web console with: systemctl enable --now cockpit.socket
Last login: Sun Nov 21 23:40:13 2021 from 192.168.1.200
[linuxteck@ftp01 ~]$
Note:
Here are the steps to disable shell access for this user.
First, create a file named "ftplogin" under the /bin directory that displays a customized login message when a restricted user attempts to shell access via ssh command."
$ sudo vi /bin/ftplogin
Add the following message to this file:
#!/bin/sh
echo -e "\x1b[31;1m\n\033[5mThis account is permitted only for FTP Service.\n\x1b[0m"
Save and close the file, then set executable permissions.
$ sudo chmod a+x /bin/ftplogin
To accomplish this, we need to insert the full path of "/bin/ftplogin" at the bottom of the "/etc/shells" file.
$ sudo vi /etc/shells
At the end of the "/etc/shells" file, you should add the following path.
/bin/ftplogin
Save and close the file. Now we need to modify the user's shell using the following command.
$ sudo usermod linuxteck -s /bin/ftplogin
Note:
As a final step, you can now try connecting to the server via ssh with the username "linuxteck" and see the output."
$ ssh linuxteck@192.168.1.100
Output:
Note:
Based on the screenshot above, we see that SSH access has been disabled for the user "linuxteck" associated with that FTP account."
Conclusion:
We have successfully configured an FTP server (vsftpd) for users with local accounts to upload/download files in Rocky Linux 8.4. Thank you for taking the time to read! We hope this article has helped you understand how it works. Drop me your feedback/comments. Feel free to share this article with others if you like it.
Thank you!